The Warning Email That Might Be a Scam
Booking.com confirmed a breach this week. Here's the most concerning part.
Booking.com sent out breach notification emails yesterday. Names, email addresses, phone numbers, and booking details were accessed by unauthorized third parties. No financial data was taken, and the company says the issue is now contained.
That’s the official summary. Here’s what the official summary doesn’t help you with.
When a breach involves booking details specifically, the follow-on scam isn’t generic phishing. It’s targeted.
A scammer who knows your name, your hotel, and your travel dates can send you a WhatsApp message that reads exactly like something your accommodation would send. Or call you, reference your reservation, and tell you there’s a payment problem with your booking.
The message will be well-written and the details will be accurate. Add it all up and the urgency will feel legitimate.
And this isn’t a theoretical scenario.
In November 2025, researchers at Sekoia documented a campaign in which attackers who had stolen hotel staff credentials used that access to contact guests over WhatsApp and email, referencing their real reservation details. The cover story was that a security issue had come up during verification of their banking details, and that confirming their information was a procedure Booking.com used to protect against cancellations. Victims who followed the link landed on a fake payment page built to look like the real thing.
The current breach didn’t involve hotel account access (thankfully). But the same logic applies: an attacker who already knows your name, your hotel, and your travel dates doesn’t need to compromise anything else to make an approach convincing.
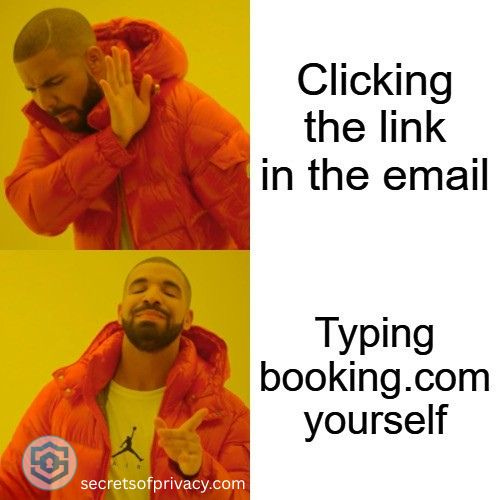
The disorienting part is that the breach notification email itself looks like the kind of thing scammers send. Plenty of people receiving a legitimate email from noreply@booking.com this week will reasonably wonder whether to trust it. Reasonably so because a decade of phishing awareness training has taught people to distrust exactly this kind of message.
The actual risk hierarchy here is worth being clear about. On the positive side, the exposed data cannot be used to make purchases or drain accounts directly. What it can do is make someone more likely to hand over payment details voluntarily, because the person asking seems to already know things only Booking.com would know.
One thing worth doing now: If you received a breach notification, or if you have an upcoming Booking.com reservation, treat any inbound contact claiming to be from Booking.com or from your accommodation as suspicious by default. That means phone calls, WhatsApp messages, and emails asking you to update payment details or “secure” your booking. If something seems urgent, navigate to booking.com directly by typing the URL and handle it from your account there. Don’t call back numbers from messages you received. Look up the number yourself.
Booking.com says it has reset PINs for affected reservations, which is a reasonable containment step. What they haven’t said is how many reservations were affected or how the access happened. That opacity is frustrating, and it’s also a pattern for them: the company was fined €475,000 by Dutch regulators in 2021 for notifying authorities too late after a previous breach.
There’s a structural question buried in all of this. Travel platforms collect a surprising amount of contextual detail about where you’re going, when, with whom, and what you’ve requested. That data is operationally necessary in the short term. Whether it needs to be retained as long as it typically is, in the form it’s stored, is a question the industry hasn’t been forced to answer seriously yet.
If you’ve had a similar experience with scam follow-up after a travel booking, I’d be curious to hear about it. Reply to this email.
Looking for help with a privacy issue or privacy concern? Chances are we’ve covered it already or will soon. Follow us on X and LinkedIn for updates on this topic and other internet privacy related topics.
Disclaimer: None of the above is to be deemed legal advice of any kind. These are *opinions* written by a privacy and tech attorney with years of working for, with and against Big Tech and Big Data. And this post is for informational purposes only and is not intended for use in furtherance of any unlawful activity. This post may also contain affiliate links, which means that at no additional cost to you, we earn a commission if you click through and make a purchase.
Privacy freedom is more affordable than you think. We tackle the top Big Tech digital services and price out privacy friendly competitors here. The results may surprise you.
Check out our new, free username generator to help you create unique usernames for different accounts. Reusing usernames is convenient, but terrible for your privacy. This tool makes it easy to create unique usernames on the fly.


Here's more on the study from Sekoia referenced in the article: https://blog.sekoia.io/phishing-campaigns-i-paid-twice-targeting-booking-com-hotels-and-customers/