How Scammers Studied a 15-Year-Old's Public Profile (Then Destroyed His Life in 3 Hours)
Sextortion scammers don't find victims randomly. They research them first.
On November 6, 2025, fifteen-year-old Bryce Tate came home from the gym, grabbed a snack, and shot some hoops in the driveway. At 4:37 PM, he received a text from an unknown number.
By 7:10 PM, he was dead.
In less than three hours, scammers had manipulated him into sending compromising photos, demanded $500, and bombarded him with 120 messages in the final 20 minutes of his life, convincing him this “one mistake had ruined his life forever.”
His father Adam later described the attackers as “godless demons” and “cowards, awful individuals, worse than criminals.” The FBI is now investigating.
It’s hard to disagree with the father’s description of the criminals. But here’s what most coverage of this tragedy misses: The scammers didn’t find Bryce randomly. They studied him first.
The Anatomy of a Targeted Attack
According to Bryce’s father, the scammers didn’t just reach out cold. They built a convincing persona based on information they gathered about his son:
“They acted like a local 17-year-old girl. They knew which gym he worked out at, they knew a couple of his best friends and name-dropped them. They knew he played basketball for Nitro High School. They built his trust to where he believed that this was truly somebody in this area.”
This is social engineering, the same technique used in phishing attacks on executives, romance scams targeting adults, and identity theft schemes. The difference is that teenagers don’t realize they’re broadcasting targeting information every time they post.
Think about what the scammers likely found on public profiles:
School affiliation from tagged locations or a bio
Sports team involvement from team photos and game posts
Friend names from tagged photos and comments
Local hangouts from gym check-ins and location tags
Daily routine patterns from when and what he posted
None of this information seems dangerous on its own. But assembled together, it creates a mosaic that makes a fake “local girl” seem completely plausible.
This Is Not Random Crime (It’s Organized)
While the FBI hasn’t disclosed specifics about who targeted Bryce, investigators noted that the messages he received bear the hallmarks of a criminal enterprise known as “764”, which is an international network with operations spanning Russia, Europe, Africa, and the United States.
This isn’t a lone scammer in a basement. The FBI is currently conducting more than 350 investigations tied to 764 and similar networks. FBI Director Kash Patel has described 764 as “modern day terrorism in America.”
Earlier this month, the Department of Justice announced indictments against five individuals in the United States connected to “Greggy’s Cult,” a 764 affiliate that prosecutors say helped spawn the larger network. Among those charged was an active-duty Navy petty officer. The youngest victim in that case was 11 years old.
These networks recruit victims through gaming platforms like Roblox and Discord, then use blackmail and psychological manipulation to extract not just money, but increasingly disturbing acts of self-harm and degradation. Members use scripts, allowing them to target dozens of children simultaneously. They can move from initial contact to blackmail in under an hour.
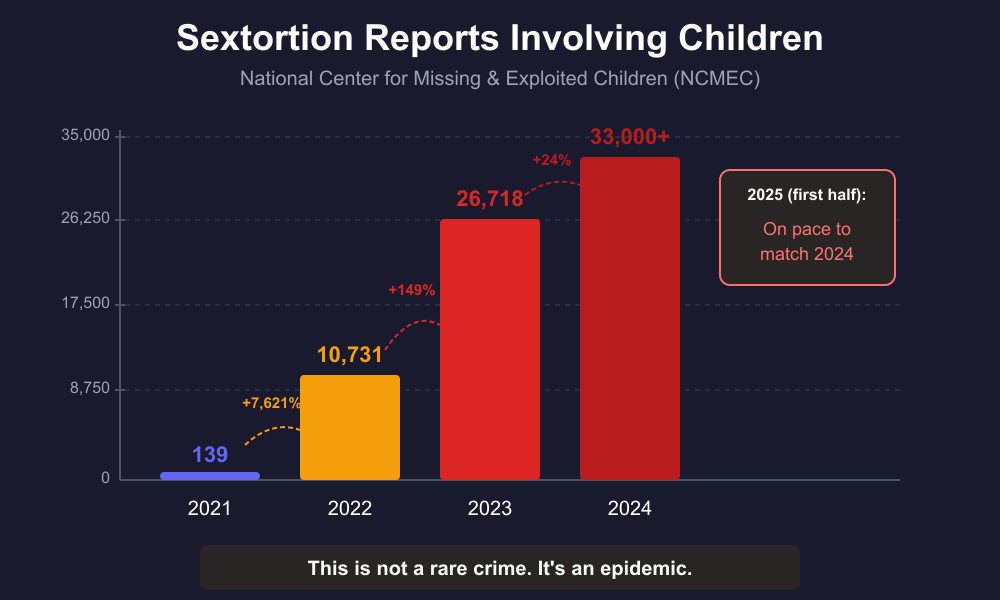
The National Center for Missing & Exploited Children logged over 33,000 sextortion reports involving children in 2024, with 2025 on pace to match. To understand how fast this exploded: in 2021, they received just 139 reports. By 2022, it was 10,731. By 2023, 26,718.
The primary targets are teenage boys aged 14 to 17, though victims as young as 8 have been identified. Between October 2021 and March 2023, the FBI documented at least 20 teen suicides connected to these schemes.
Why This Is a Privacy Problem
The standard advice around sextortion focuses on telling kids not to send nude photos. That’s important, but it treats sextortion as purely a decision-making problem.
The attack actually starts much earlier, before any photos are exchanged.
Here’s the real vulnerability chain:
Public profile → Scammer identifies a target
Public information → Scammer builds a fake persona with local details
Trust established → Teen believes they’re talking to someone nearby who knows their friends
Compromising photos obtained → Extortion begins
The typical advice only addresses step 4. But if you can disrupt steps 1 and 2 (by reducing what’s publicly available) you make it much harder for the scam to ever gain traction.
You can’t effectively social engineer someone you know nothing about.
What You Can Actually Do
We’re not going to tell you to confiscate your teen’s phone or delete all their social media accounts. That’s not realistic if you’re already let them have phones and social media access (we personally advise against giving teens social media access). It’s also likely to backfire, creating conflict and driving their online activity underground where you have even less visibility.
Instead, think of this as harm reduction.
The goal is to make your teen a harder target without blowing up your household. Some of these steps you can do together. Some you might just suggest. All of them reduce the information available to someone trying to build a fake persona.
Start with the low-hanging fruit.
The easiest change (and probably the most impactful) is switching accounts from public to private. On Instagram, TikTok, and Snapchat, this single setting means only approved followers can see posts. It doesn’t restrict who your teen can talk to or what they can post; it just limits the audience to people they’ve accepted.
Most teens won’t resist this one if you frame it right: “You’re not in trouble, and I’m not trying to spy on you. I just learned about how scammers research kids before targeting them, and I’d feel better if random strangers couldn’t see everything you post.”
Suggest a bio cleanup.
A lot of teens have identifying information sitting right in their profile bio, such as school name, graduation year, sports teams, city. This is exactly what scammers use to appear local and legitimate.
You don’t need to demand they remove it. Just point out the risk: “Did you know scammers look at bios to figure out where kids go to school so they can pretend to be someone nearby?” Let them decide what to take out.
Talk about location tagging.
Many teens reflexively tag their location on posts or have location services enabled without thinking about it. Gym check-ins, school tags, and “currently at” posts create a map of their routine.
This is a good conversation to have rather than a setting to change behind their back: “When you tag your location, anyone can see where you hang out and when. That’s how those scammers knew which gym that kid worked out at.”
Review the follower list together.
If your teen has a public account (or had one in the past), they may have followers they don’t actually know. Suggest going through the list together and removing anyone unfamiliar.
Again, framing matters: “I’m not trying to control who your friends are. I just want to make sure you actually know the people who can see your stuff.”
Know what platforms they’re on.
Sextortion doesn’t just happen on Instagram. Gaming platforms like Discord, Roblox, and various chat apps are common entry points. In fact, prosecutors say the 764 network specifically recruits victims through gaming platforms. You don’t need to monitor every conversation, but you should at least know what apps are installed and have a general sense of where they spend time online.
Consider device location, gently.
Many sextortion attempts happen late at night when teens are alone in their rooms. Some families have success with a “devices charge in the living room” policy that creates a natural nighttime boundary without being punitive.
This one depends heavily on your teen’s age and your household dynamics. For younger teens, it’s reasonable. For older teens, it might feel infantilizing. Use your judgment.
One of the best defenses against sextortion is setting up strong privacy and communication boundaries on your children’s devices from day one, before risky patterns develop. If you have a younger child getting their first iPhone, we created a free mini-course that walks through privacy-first setup and communication limits that establish these boundaries early. Access the course for free in our digital shop or on YouTube. Here’s the intro to the program.
The Conversation That Matters Most
All of the privacy settings in the world won’t help if your teen doesn’t feel safe coming to you when something goes wrong.
Bryce Tate had his last $30 in his account. He sent it to the scammers and begged for more time. He didn’t tell his parents because he believed, in the panic of the moment, that his life was ruined.
His father later said: “You cannot find a closer family than me, my wife, and my son. But I just want people to know that having that safe space and that close family is not enough. They have to be aware of what the threat is.”
The most important thing you can do is have a conversation before anything happens. Make it clear:
If anyone ever threatens you online, for any reason, you tell me immediately.
You will not be in trouble for coming forward.
These are professional criminals running this scam on thousands of kids. It’s not personal, and one mistake doesn’t ruin your life.
We can block them, report them, and move on. It will be okay.
Have this conversation when everything is fine and not as a reaction to something scary. Normalize it. Make it part of how your family talks about being online.
What To Do If It Happens
If your teen comes to you (or you discover) that they’re being extorted, the first priority is stopping the panic spiral. That’s what these criminals exploit: the overwhelming shame and fear that makes victims feel like there’s no way out.
Don’t panic. Here’s the process.
Panic happens when uncertainty hits faster than your brain can sort it. The fix isn’t “calm down” (that never works), it’s giving yourself a simple sequence to follow.
Check out this great post that provides a three part panic killing method:
Here’s a short version:
Name what’s happening: “Someone is trying to blackmail my kid. This is a crime being committed against us, not something we did wrong.”
Identify the first small step: Not “solve the whole problem,” just “what’s the one thing that improves our position right now?” Usually that’s: stop responding.
Execute immediately: The body calms down after it sees you take control, not before. Action restores traction.
Here’s the practical sequence:
Stop all communication. Block the account and don’t engage further. Every response gives them more leverage. This is the single most important immediate action.
Don’t pay. Payment never stops the threats. Scammers escalate or continue targeting victims even after receiving money. Paying signals that the victim is responsive and may have access to more.
Screenshot everything first. Before blocking, preserve evidence of the threats, the account, and any messages. This helps law enforcement.
Report it. File reports with:
The FBI: tips.fbi.gov or 1-800-CALL-FBI
NCMEC’s CyberTipline: CyberTipline.org
Local police
The platform where it occurred
Use Take It Down. This free service from NCMEC (takeitdown.ncmec.org) helps remove or prevent the sharing of explicit images of minors. It works even if images have already been shared.
Reassure your teen (repeatedly). The person who sent photos is not in trouble with law enforcement, the criminals are. Your teen needs to hear, clearly and often, that this doesn’t define them, that it’s survivable, and that reporting helps stop these people from hurting other kids.
The shame these criminals weaponize is the most dangerous part of the attack. Counter it directly.
The Privacy Lesson Here
The same principles that protect you from data brokers, identity theft, and social engineering apply to your children. Reducing your digital footprint isn’t only for the paranoid. With today’s threats, it’s a basic step to enhance personal protection.
Scammers targeted Bryce Tate because they could. His public profile gave them everything they needed to build a convincing fake persona. A private account, a cleaner bio, and fewer location tags wouldn’t have made him immune. But it would have made him a harder target. And criminals looking for easy victims tend to move on to easier marks.
Start where you can. Have the conversation. Make the settings changes that won’t cause a fight. Plant the seed about why this matters.
It might be the most important privacy audit you ever do.
Resources
For Parents:
FBI Sextortion Resources: fbi.gov/sextortion
NCMEC Take It Down Service: takeitdown.ncmec.org
FBI Parent/Caregiver Guide: fbi.gov/how-we-can-help-you/parents-and-caregivers-protecting-your-kids
If It’s Happening Now:
FBI Tips: tips.fbi.gov or 1-800-CALL-FBI
NCMEC CyberTipline: CyberTipline.org
Crisis Resources:
National Suicide Prevention Lifeline: 988
Crisis Text Line: Text HOME to 741741
Friendly Ask
If you found this helpful or informative, chances are your friends and family will as well. Please share it with them to help spread awareness.
Looking for help with a privacy issue or privacy concern? Chances are we’ve covered it already or will soon. Follow us on X and LinkedIn for updates on this topic and other internet privacy related topics.
Disclaimer: None of the above is to be deemed legal advice of any kind. These are *opinions* written by a privacy and tech attorney with years of working for, with and against Big Tech and Big Data. And this post is for informational purposes only and is not intended for use in furtherance of any unlawful activity. This post may also contain affiliate links, which means that at no additional cost to you, we earn a commission if you click through and make a purchase.
Privacy freedom is more affordable than you think. We tackle the top Big Tech digital services and price out privacy friendly competitors here. The results may surprise you.
Check out our new, free username generator to help you create unique usernames for different accounts. Reusing usernames is convenient, but terrible for your privacy. This tool makes it easy to create unique usernames on the fly.
Do you own a Smart TV? If so, you won’t want to miss this reader fav post Smart TV Privacy Settings: How to Disable Tracking on Every Brand.
If you’re reading this but haven’t yet signed up, join for free (4.3K+ subscribers strong) and get our newsletter delivered to your inbox by subscribing here 👇